Overview
This is part 5 in our SharePoint 2013 ADFS 3.0 Installation and Configuration series of articles. In this article we will discuss the setup of a relying party within ADFS for use with our SharePoint 2013 farm.
- SharePoint 2013 and ADFS 3.0 Installation Guide
- Part 1: Lab Environment
- Part 2: Install Windows Certificate Authority
- Part 3: ADFS Prerequisites
- Part 4: How to Install and Configure ADFS 3.0
-
Part 5: Configure Relying Party in ADFS 3.0
- Part 6: Configure Web Application for ADFS
- Part 7: Configure User Profile Service for ADFS
- Part 8: Validate Configuration with “Claims Viewer Web Part”
- Supplemental 1: Configure People Picker to resolve ADFS Identities
- Supplemental 2: Adding Host Name Site Collections to Existing Web Application Configured to use ADFS
- Supplemental 3: Configure Automatic Sign-In with Mixed Authentication
Configure a Relying Party
In our previous article we installed and configured ADFS. Now that ADFS is setup we can configure the initial “Relying Party” to be used with our SharePoint web application “spt.splab.local”
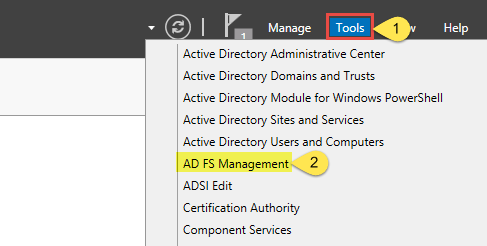
- Start the “AD FS Management” console from the Tools menu in Server Manager
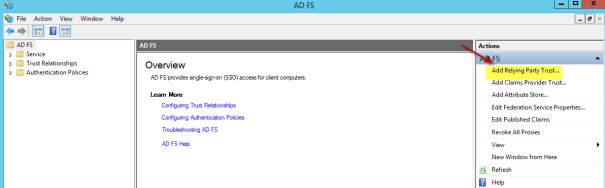
- Click the “Add Relying Party Trust” link in the “Overview” section of the AD FS console
- Click “Start” on the welcome screen
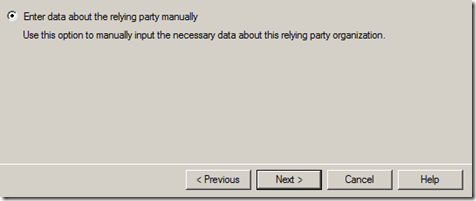
- Select the “Enter data about the relying party manually” radio button and click “Next >“
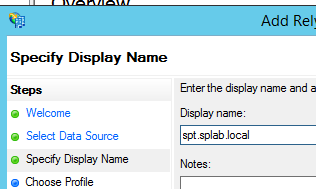
- Enter a value in the “Display name:” and optionally the “Notes:” fields
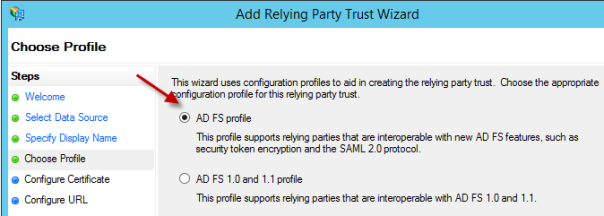
- Select the “AD FS profile” radio button and click “Next >“
- Click “Next >” on the “Configure Certificate” screen because it is not necessary to encrypt SAML tokens since HTTPS is a requirement for the SharePoint Web App to communicate with the ADFS STS
- Select the “Enable support for the WS-Federation Passive protocol” checkbox and enter the URL for the relying party WS-Federation Passive protocol URL then click “Next >“
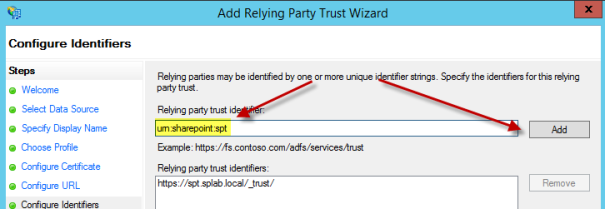
- Enter a relying party trust identifier and click the “Add” button
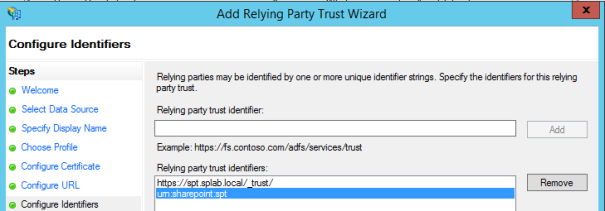
- Verify it has been added and then click “Next >“
- Select the “I do not want to configure multi-factor authenticatoin settings for this relying party trust at this time.” radio button and then click “Next >“
- Select the “Permit all users to access this relying party” radio button and then click “Next >“
- Review the configured settings and click “Next >“
- Leave the “Open the Edit Claim Rules dialog for this relying party trust when the wizard closes” and click “Close“
Add Claims Rule
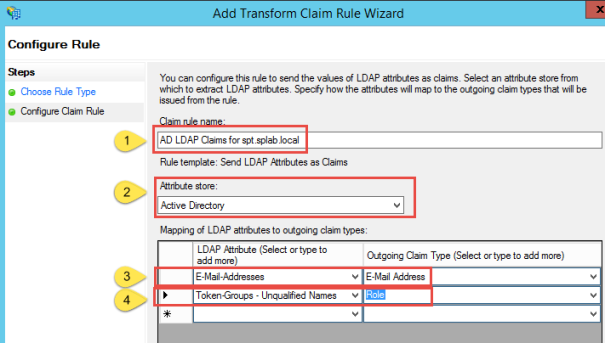
In this step a claim rule will be created that maps email address and role attributes from Active Directory.
- Click “Add Rule…“
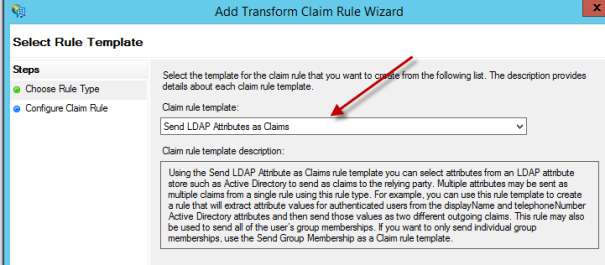
- Select the “Send LDAP Attributes as Claims” entry from the dropdown box and click “Next >“
- Enter a “Claim rule name:“, select “Active Directory” for “Attribute store:” and configure the attribute mapping. Click “Finish” when done and then “OK” to accept.
- The relying party is now configured and will be used in subsequent steps when configuring a “Trusted Authentication Provider” in SharePoint

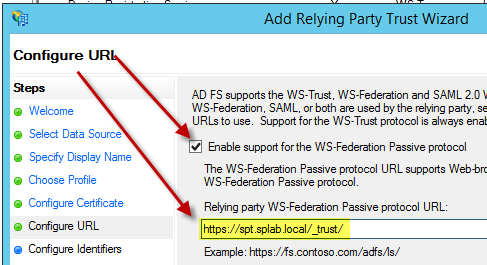
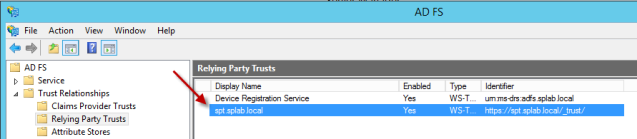
I believe the URL for Relying Parties is wrong, should be https://spt.splab.local/_trust
not https://spt.splab.local//trust_
You are correct! I’ll have to update my screenshots. Thanks for the catch!
Its all updated now. Thanks for the proofreading!